Building an Unstoppable Security Team: Insights from Christian Hyatt's Security Team Operating System
In the ever-evolving landscape of cybersecurity, building and managing an effective security team is crucial for organizations to protect themselves against emerging threats. Recently, G Mark Hardy, host of the CISO Tradecraft podcast, sat down with Christian Hyatt, author of "The Security Team Operating System: Five Secrets to Build a Security Team that Doesn't Suck," to discuss strategies for creating high-performing security teams.
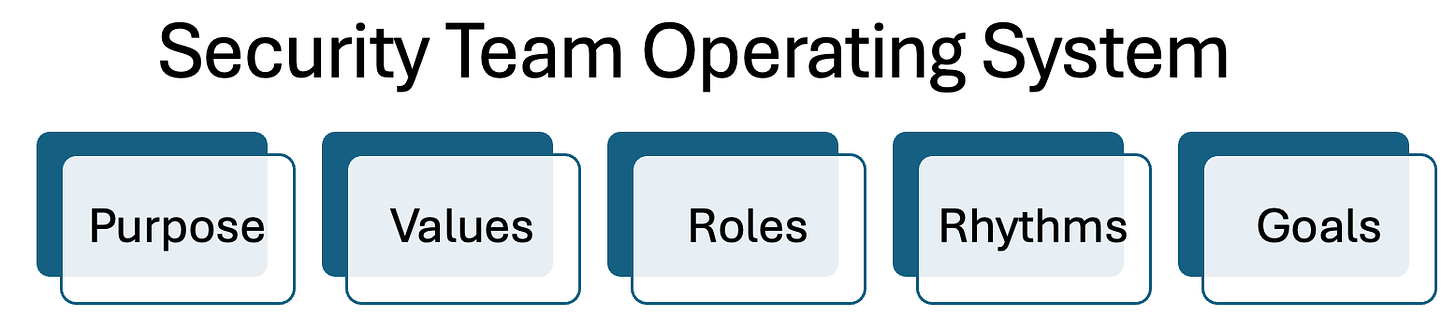
The Security Team Operating System (STOS) Framework. Hyatt's STOS framework consists of five key components:
Let's dive deeper into each of these elements and explore how they contribute to building a robust security team.
Purpose: Aligning with Business Objectives
The first and perhaps most critical component of the STOS framework is purpose. Hyatt emphasizes the importance of aligning the security team's objectives with the broader business goals. This alignment ensures that security efforts are not only effective but also contribute meaningfully to the organization's success.
Hyatt shares an example of a private equity-backed company where the primary mission was to reduce costs while maintaining essential security and compliance requirements. By clearly defining these dual objectives, the security leader was able to guide their team's efforts more effectively, cutting unnecessary projects and finding efficiencies that aligned with the company's goals.
To achieve this alignment, Hyatt suggests several practical approaches:
1. Having conversations with business leaders
2. Reading company financial reports (e.g., 10-K for public companies)
3. Staying attuned to management's actions and priorities
Hyatt stresses that security leaders must have the courage to engage in difficult conversations with business leaders to truly understand organizational priorities. This understanding allows security teams to focus their efforts on initiatives that genuinely move the needle for the business.
Values: Building a Strong Team Culture
The second component of the STOS framework focuses on establishing clear values that reinforce desired behaviors within the organization. While some security leaders may view this as a "mushy" concept, Hyatt argues that defining core values is essential for several reasons:
1. It helps in hiring the right people who align with the team's culture
2. It provides a framework for holding team members accountable
3. It guides decision-making processes
Hyatt shares his company's approach to hiring, which involves evaluating candidates based on their alignment with core values in addition to their technical skills. This method has proven effective in building a cohesive team culture.
For security leaders looking to define their team's values, Hyatt recommends:
1. Aligning with existing organizational values when possible
2. Identifying specific behaviors that support those values
3. Involving the team in the process of defining and refining values
Roles: Structuring for Success
Roles: Create Clearly Defined Accountability
The third element of the STOS framework addresses the importance of clearly defined Roles within the security team. While some may worry that tightly defined roles could limit growth opportunities, Hyatt argues that clarity in responsibilities is crucial for accountability and effective team management.
Hyatt suggests thinking of roles not as rigid job descriptions, but as "things that need to get done." This approach allows for flexibility while still providing a clear understanding of responsibilities. He emphasizes that the goal is to achieve clarity in the organization, which can inform hiring plans, delegation decisions, and process documentation.
To implement this component effectively, security leaders should:
1. Map out all necessary functions within the security team
2. Identify any overlaps or gaps in responsibilities
3. Use this information to guide hiring, delegation, and professional development decisions
Rhythms: Establishing Predictable Cadences
The fourth component of the STOS framework focuses on creating predictable rhythms or cadences for communication and accountability within the team. Hyatt argues that establishing these rhythms is crucial for reducing anxiety, improving communication flow, and harnessing the team's energy effectively.
Some examples of rhythms that Hyatt recommends include:
1. Annual offsites for forward-looking planning
2. Quarterly onsite meetings for retrospectives and short-term planning
3. Weekly all-hands meetings for news and energy-boosting
4. Mid-year and end-of-year performance reviews
By implementing these rhythms, security teams can create a sense of predictability and clarity, which helps team members plan their work more effectively and reduces anxiety caused by ad-hoc communication and decision-making.
Goals: Driving Intentional Progress
The final component of the STOS framework is setting clear, actionable goals. Hyatt emphasizes the importance of aligning individual and team goals with the broader organizational objectives. He uses the analogy of a shaped charge explosive to illustrate how focused energy (in the form of well-defined goals) can produce outsized results.
To set effective goals, Hyatt recommends:
1. Ensuring that department and individual goals nest within broader organizational objectives
2. Using the SMART (Specific, Measurable, Achievable, Realistic, Time-bound) framework for goal-setting
3. Coaching managers to help team members set goals that align with both personal and professional development
Implementing the STOS Framework
While the STOS framework offers a comprehensive approach to building and managing security teams, Hyatt acknowledges that implementation can be challenging. He offers two key pieces of advice for security leaders looking to adopt this framework:
1. Accept imperfection: Recognize that implementing the framework is a journey, and it's okay to start with a partial solution and iterate over time.
2. Avoid overthinking: Don't let the pursuit of perfection prevent you from taking action. Start with what you can do now and improve as you go.
Hyatt also argues that implementing the STOS framework can lead to cost savings by ensuring that resources are focused on initiatives that truly matter to the business. By aligning security efforts with business objectives, teams can eliminate waste and more easily justify budget requests.
Conclusion
Building an effective security team is a critical challenge for modern organizations. Christian Hyatt's Security Team Operating System framework offers a structured approach to addressing this challenge, focusing on purpose, values, roles, rhythms, and goals. By implementing these five components, security leaders can create teams that are not only technically proficient but also aligned with business objectives and equipped to adapt to the ever-changing threat landscape.
As Hyatt reminds us, the journey to building a great security team is ongoing. The key is to start the process, embrace iteration, and continually strive for improvement. By doing so, security leaders can create teams that are not just reactive, but truly unstoppable in their mission to protect their organizations.