Stop Buying Vaporware: The CISO’s Guide to Murdering Waste and Doubling Your Budget Success
If you’re walking into budget season feeling like you’re constantly fighting for crumbs while the company is still exposed to risk, you’re not alone. Many organizations invest millions in cybersecurity only to still suffer breaches, proving that simply throwing more money at the problem is not the solution.
Ross Young, a 20-year veteran of cybersecurity whose experience includes 10.5 years at the CIA, time at Capital One during a large-scale data breach, and four years as CISO at Caterpillar Financial, argues that leaders must shift their perspective. Instead of focusing solely on technical metrics, CISOs must focus on maximizing the outcomes per dollar spent.
This requires financial fluency and a new mental model. Here are the most essential, hard-hitting recommendations CISOs can implement today to secure budgets, eliminate waste, and transform their security posture.
1. Adopt the Mantra: Cybersecurity is Revenue Protection
Too often, CISOs are stuck in the mindset of protecting bits and bytes. The crucial shift is recognizing that cybersecurity is the business of revenue protection. If a company spends a billion dollars on cyber and only generates a billion dollars in profit, the spending is unsustainable.
Recommendation for CISOs:
Financial Literacy Over Nerdy Metrics: Stop focusing purely on security metrics when presenting to executives. Frame your needs around the financial health and continuity of the business. Your job is to enable the executive team to make informed, risk-based decisions.
The Six-Shooter Prioritization: Avoid the common pitfall of a diluted resource problem where you try to fix 50 things at once. Instead, identify the six critical things you must accomplish this year and constantly reinforce those priorities in every meeting. This focused approach ensures your efforts are not diluted and you accomplish much more.
2. Treat Compliance Like a Pass/Fail Exam
When analyzing where security dollars go, investments fall into two clear buckets: Risk Reduction (money spent on tools proven to stop attacks, like email security gateways) and Compliance (money spent on required regulations, contracts, or third-party agreements).
The harsh reality is that time spent writing policies or producing evidence for compliance does not stop the next breach. No bad actor is reading your InfoSec policy.
Recommendation for CISOs:
Minimize Compliance Effort: Treat compliance activities, such as a SOC 2 attestation or audit, as purely pass/fail. Once you have presented enough evidence (which might be one screenshot rather than a 20-page report) to satisfy the requirement, stop spending time on it.
Reallocate Headcount: Spending excessive time trying to squeeze out extra effort on compliance takes away valuable labor hours that could be dedicated to material risk reduction—the activities that actually stop attacks.
3. Don’t Drink the Quantification Kool-Aid: Go Qualitative
One of the most insidious sources of wasted time and money is blindly pursuing Cyber Risk Quantification (CRQ). Young cautions that CRQ often relies on “vague math times uncertain math,” which yields unreliable and vague risk measurements. We often lack the 20 years of historical data necessary to accurately estimate complex likelihoods, such as the material loss expected from AI harming a company.
This excessive mathematical exercise can cost companies millions and thousands of hours, ultimately destroying the CISO’s credibility when the numbers are unbelievable.
Recommendation for CISOs:
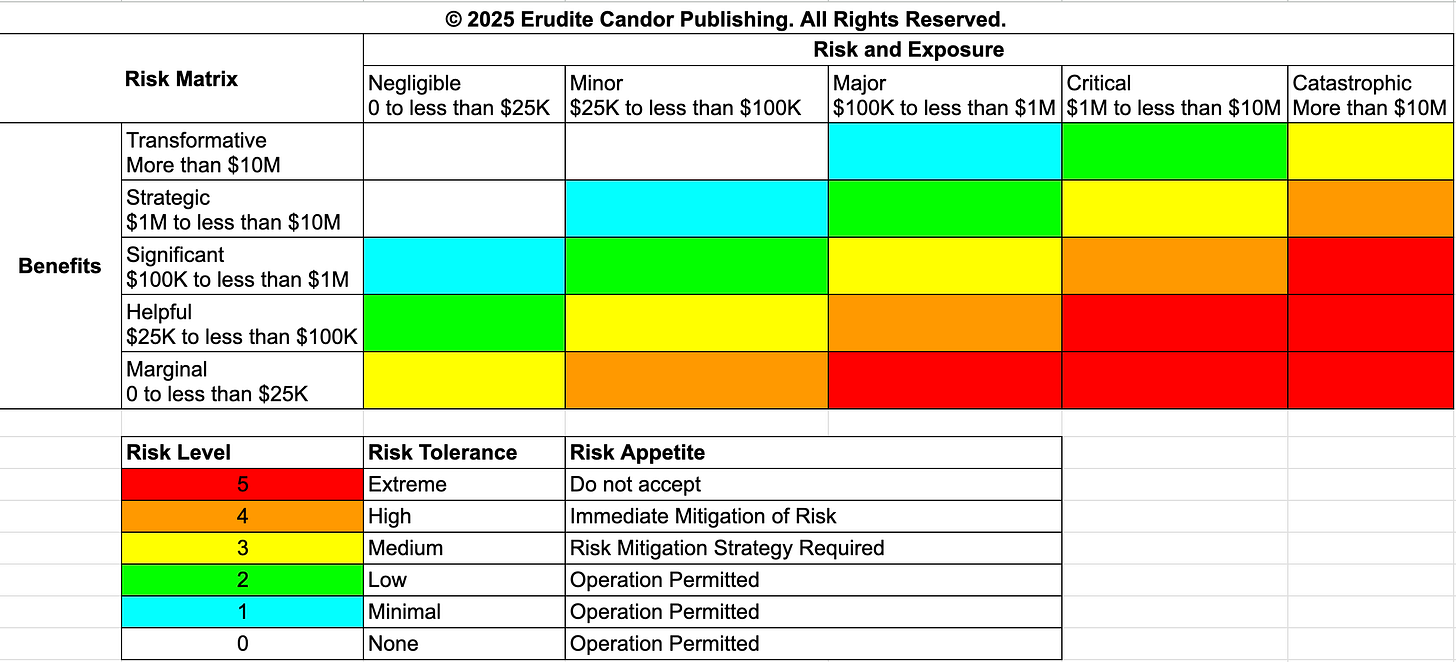
Embrace Qualitative Analysis: Instead of bickering over exact figures like “93.27% likelihood,” adopt a qualitative approach using orders of magnitude.
Align Risk to Procurement Authority: In your first 90 days, ask the Chief Financial Officer (CFO) how much various levels of leadership (Manager, Director, VP) are authorized to spend on corporate procurement (e.g., $50,000, $500,000, $5 million).
Standardize Decision-Making: Apply these same financial brackets to risk acceptance. This creates a decision-making process that aligns with the rest of the business—a manager accepts risks between $0 and $50,000, and a VP accepts risks up to $5 million. This saves thousands of hours of unnecessary analysis and still allows for effective prioritization.
4. Master Financial Kung Fu with Total Cost of Ownership (TCO)
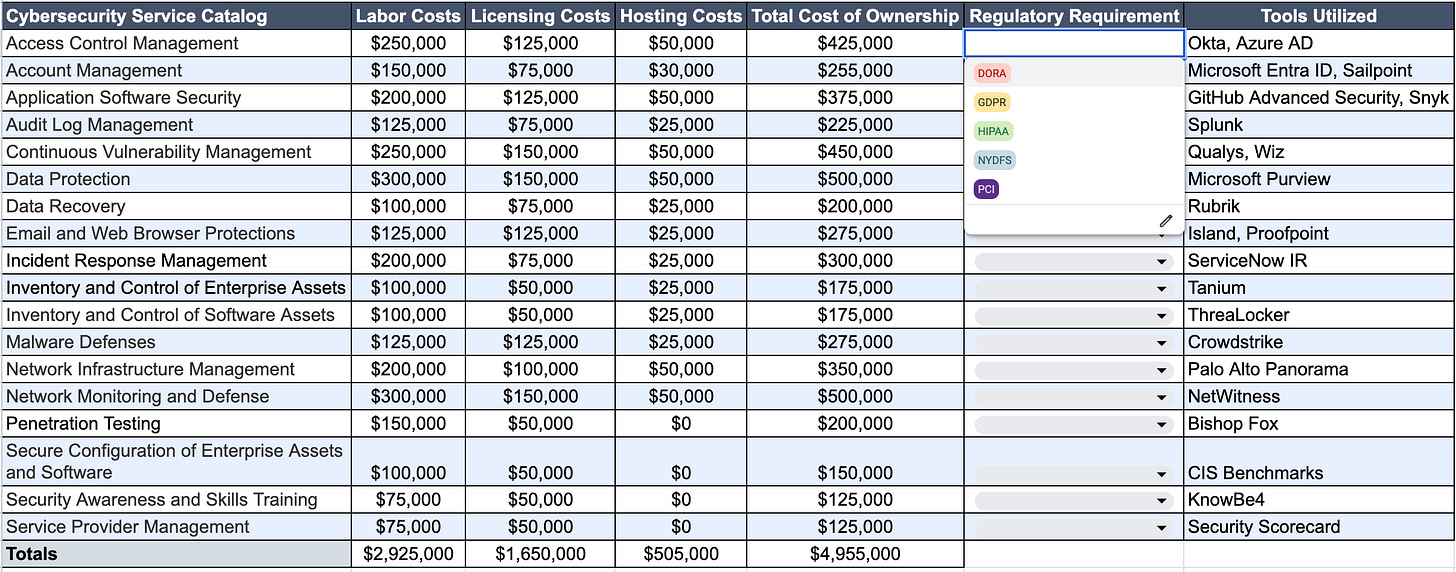
To strategically manage spending, move beyond the traditional CapEx and Opex model and adopt Total Cost of Ownership (TCO). This zero-based budgeting approach provides a strong approximation of cybersecurity spending by breaking it into three levers for every IT application:
Labor Costs: The cost of developers/staff supporting the application.
Licensing Costs: Fees paid to vendors (e.g., Oracle or SaaS providers).
Hosting Costs: Fees paid to cloud providers (e.g., AWS).
Recommendation for CISOs (The TCO Formula):
Maximize Value through Leverage: Use TCO to demonstrate ROI. For instance, you can justify a $200K license purchase if it allows you to reduce the labor costs associated with supporting an open-source tool by three people, resulting in a net cost saving exceeding $200K.
Split Labor for Justification: Split Labor Costs into two categories: New Features and Operations and Maintenance. These must always total 100%.
Justify Upgrades by Cutting Maintenance: Actively look for legacy applications where 90% of labor time is consumed by maintenance (a sunk cost). Propose an upgrade that cuts maintenance time (say, to 30%), freeing up 60% of the team’s time to build new features. This financial “kung fu” shows the CFO an immediate ROI: you can fund a million-dollar upgrade by demonstrating how saving six headcount (if they cost $100K each, saving $600K) makes the project financially viable over a short period.
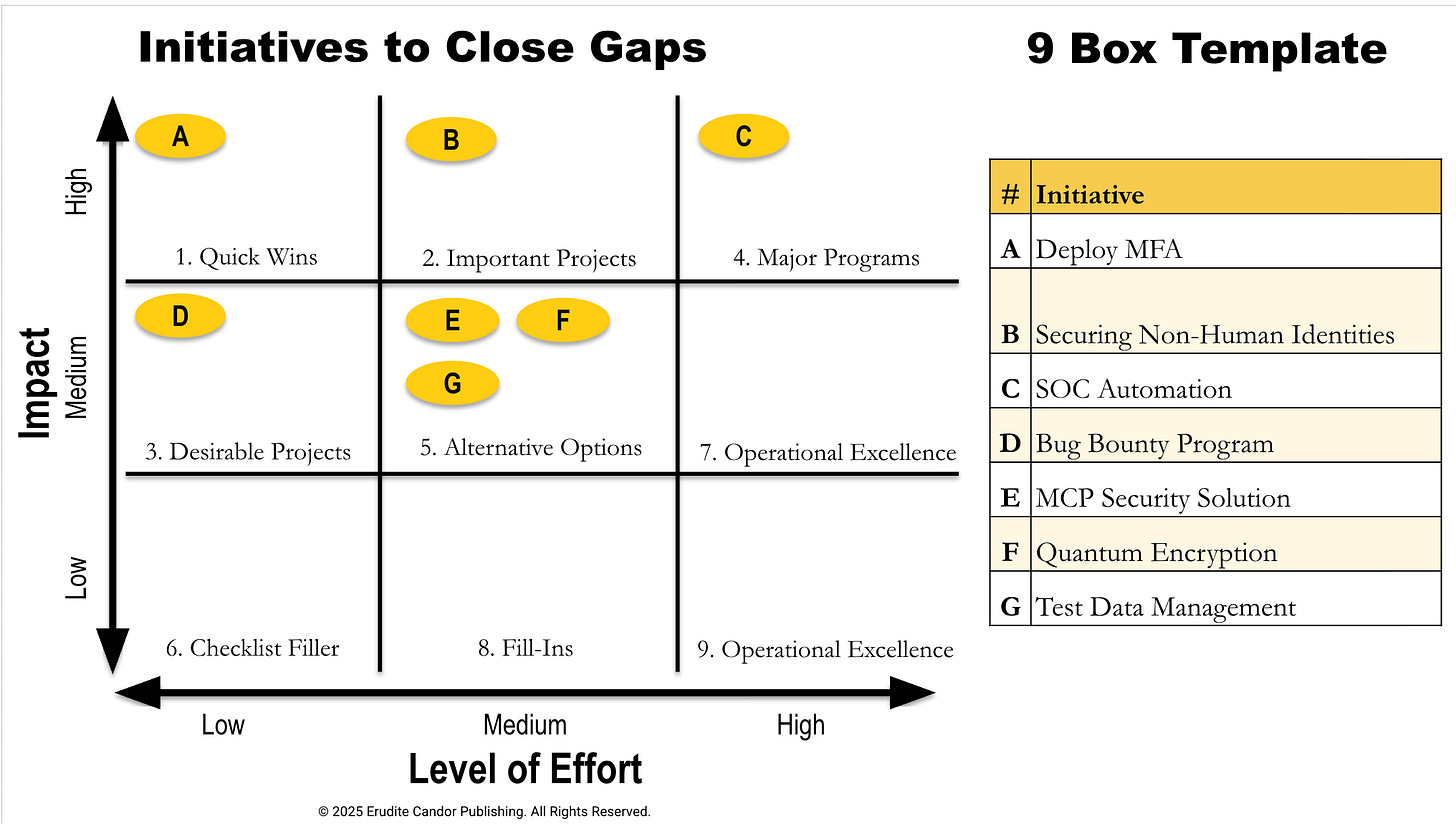
5. Prioritize with Precision: The 9-Box Template
When faced with 50 potential projects but only enough budget for 15, the 9-Box Template is indispensable for strategic prioritization.
Recommendation for CISOs (Applying the 9-Box):
Define the Axes: Plot every project on an XY axis defined by Level of Effort and Impact (Material Risk Reduction).
Level of Effort: Low (<90 days), Medium (90 days–1 year), or High (>1 year).
Impact (Material Risk Reduction): This value is organizational specific (e.g., high hundreds of millions at Bank of America, tens of thousands at an SMB), but the concept remains constant.
Hunt for Quick Wins: Prioritize high-impact projects that require low effort (solved in less than 90 days).
Avoid the Drag: Projects that show low material risk reduction and require high effort should generally be avoided unless specifically mandated by a regulator. (The 9-Box template is available as a free download on the CISO Tradecraft website).
6. End Meeting Waste and Murder Useless Tools
Labor hours lost to inefficient processes are a major source of financial waste and opportunity cost. Young notes, “being busy is the new stupid,” and studies show that over 30% of executive time is consumed by meeting waste.
Recommendation for CISOs (Labor Discipline):
Implement Strict Meeting Rules: Start with simple discipline: ensure every meeting has a detailed agenda. Only decision-makers should be invited, eliminating “filler” attendees.
Calculate the Cost: Use tools to calculate the financial cost of a meeting (e.g., a $10,000 meeting) and determine if the value generated exceeds that expense. If leaders consistently start exactly on time, people will adapt their behavior to ensure they are present for critical decision points.
Recommendation for CISOs (Tool Optimization):
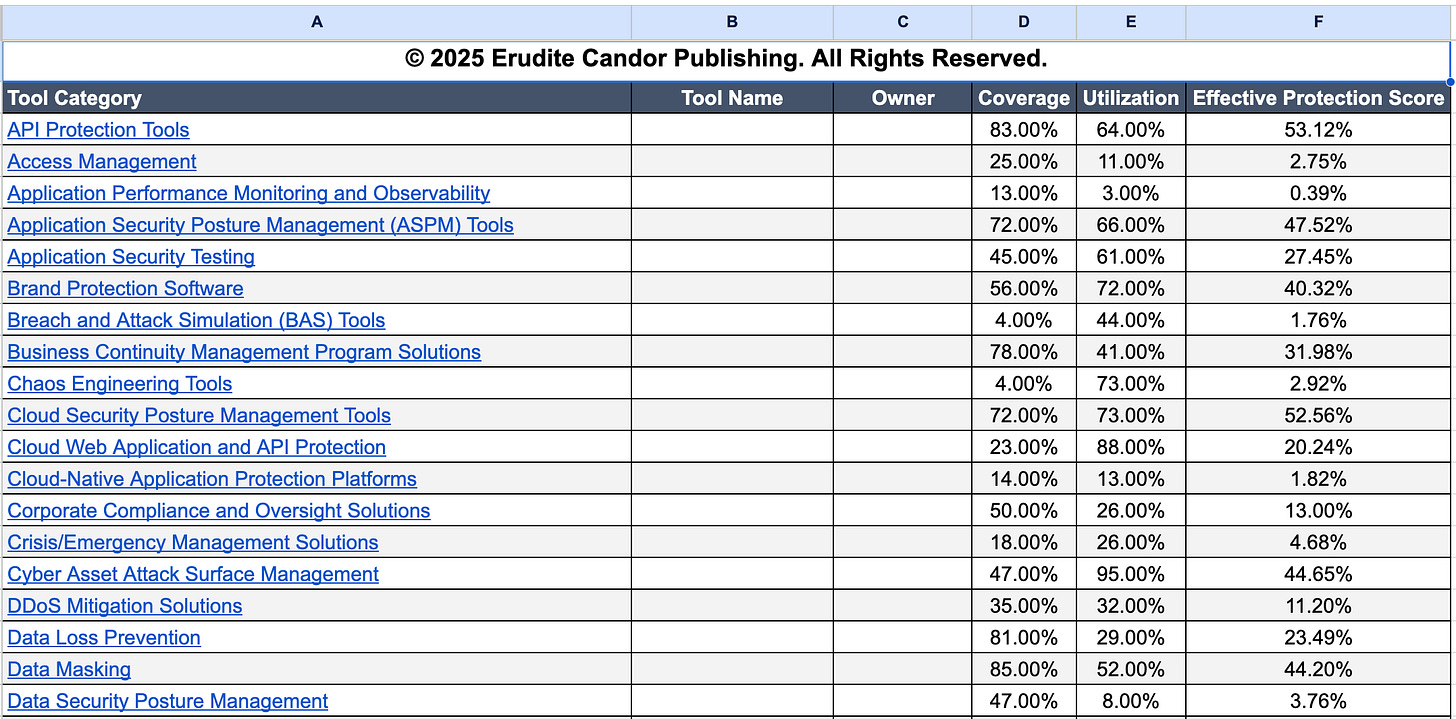
Assess Effective Protection Score: Use quantitative methods to check the effectiveness of your existing tools before buying new ones. For example, if you purchased a DLP tool, but only deployed it on 50% of endpoints, and only half of the features are turned on, your effective protection score is only 25% (50% x 50%).
Fix or Fire: If tools are not well configured or deployed, resources are diluted, and you are not getting the coverage needed. If a tool doesn’t actively stop attacks and isn’t solving a clear compliance requirement, get rid of it and “Murder that tool.” It is not delivering the value you think it is.
7. Master the CFO Pitch: Speak Revenue
If you are asking for an increase in budget, you must speak the language of the CFO: financial literacy and business impact.
Recommendation for CISOs:
Tie Spend Directly to Revenue: Do not present a security certification merely as a compliance necessity. Connect the investment directly to the business pipeline.
Example in Action: If achieving ISO 27001 certification costs $30K, explain that this certification is required by 30 customers who generate $30 million of revenue. When framed this way, the CFO is not risking $30 million for the sake of avoiding a small $30K expense, making the decision to approve the funds immediate: “Make this go away. Yes. Get that ISO 27,001 certification”.
Highlight Resilience: Emphasize that your investments enable the business to succeed and provide resilience for the IT infrastructure, which is critical for success—unlike, for example, maintaining expensive, underutilized physical office space.
By implementing these structural, financial, and prioritization disciplines, CISOs can transform themselves from a perceived cost center into a crucial partner focused on protecting the company’s financial success.
Ross Young’s insights and strategies are compiled in his upcoming book, Cybersecurity’s Dirty Secret, expected to be released before the end of the year. For CISOs ready to implement these 30 budget-maximizing concepts immediately, the comprehensive course, “Mastering the Budget,” which includes all templates and video guidance, is available now at CISOTradecraft.com.